A BYOD (Bring Your Own Devices, azaz „hozd magaddal a saját eszközödet”) lehetővé teszi a munkavállalók számára, hogy saját számítógépeiket, okostelefonjaikat vagy egyéb eszközeiket használják a munkához. Első ránézésre ez egy olyan helyzet, amelyben mindenki nyer. A munkavállalók olyan eszközökön dolgozhatnak, amelyeket jól ismernek, így már az első naptól kezdve javul a termelékenységük. A munkáltatók pedig pénzt takarítanak meg a hardverköltségek csökkentésével.
Egyes kiberbiztonsági körökben azonban a BYOD-ot tréfásan „hozd magaddal a saját katasztrófádat” (bring your own disasters) néven emlegetik. Ha a BYOD-ot biztonsági szempontból vizsgáljuk, a kérdés már árnyaltabbá válik. Amennyiben a munkavállalók személyes eszközeiket használják a munkavégzéshez, a szervezeteknek gondoskodniuk kell arról, hogy ezek az eszközök megfeleljenek az alapvető biztonsági előírásoknak, mint például a frissített operációs rendszer, a végpontok védelme, a titkosítás és egyebek.
A magáncélú eszközöket kiszámíthatatlan módon használják, ami megnehezíti a biztonsági előírások betartatását azokon a készülékeken, amelyek nem a vállalat tulajdonát képezik. Az alkalmazottak a közösségi médiától a filmnézésig mindenre használják ezeket az eszközöket. Előfordul, hogy megosztják őket családtagjaikkal vagy barátaikkal. A vállalati biztonsági eszközök nem tudják megkülönböztetni, mely tevékenységek kapcsolódnak a munkához, és melyek nem.
Mivel a szervezetek nem rendelkeznek saját hardverrel, és azt sem ellenőrzik, az informatikai csapatok nem tudhatják, hogy milyen alkalmazások vannak telepítve, milyenek a biztonsági beállítások, illetve milyen hálózati tevékenységek folynak. Ez az úgynevezett „árnyék-IT” jelenséghez vezet, amelynek során nem felügyelt, nem biztonságos eszközök férnek hozzá az érzékeny vállalati adatokhoz, növelve ezzel az adatszivárgás, a rosszindulatú szoftverek és a felderítetlen biztonsági incidensek kockázatát.
A magán- és a szakmai használat közötti átfedés nyilvánvaló adatvédelmi aggályokat vet fel, mivel a vállalat által kezelt, folyamatosan futó felügyeleti szoftverek tolakodónak tűnhetnek. Ha incidensek történnek, a BYOD bonyolítja a kockázatcsökkentést. Általában egy fertőzött vállalati eszközt el lehet szigetelni, elemezni és kicserélni, de egy magánlaptoptól vagy mobiltelefontól ezt nem olyan egyszerű megkövetelni.
Előfordulhat, hogy az alkalmazottak érzékeny fényképeket, pénzügyi adatokat vagy magánjellegű levelezést tárolnak ugyanazon az eszközön, ezért vonakodhatnak attól, hogy átadják azt. Bizonyos joghatóságok alatt akár törvényes joguk is van az átadás megtagadására. Egy megfertőzött személyes eszköz azonban bejáratot nyithat a szervezet legkritikusabb rendszereihez vagy érzékeny adataihoz, ami súlyos következményekkel járhat.
Hol van a középút?
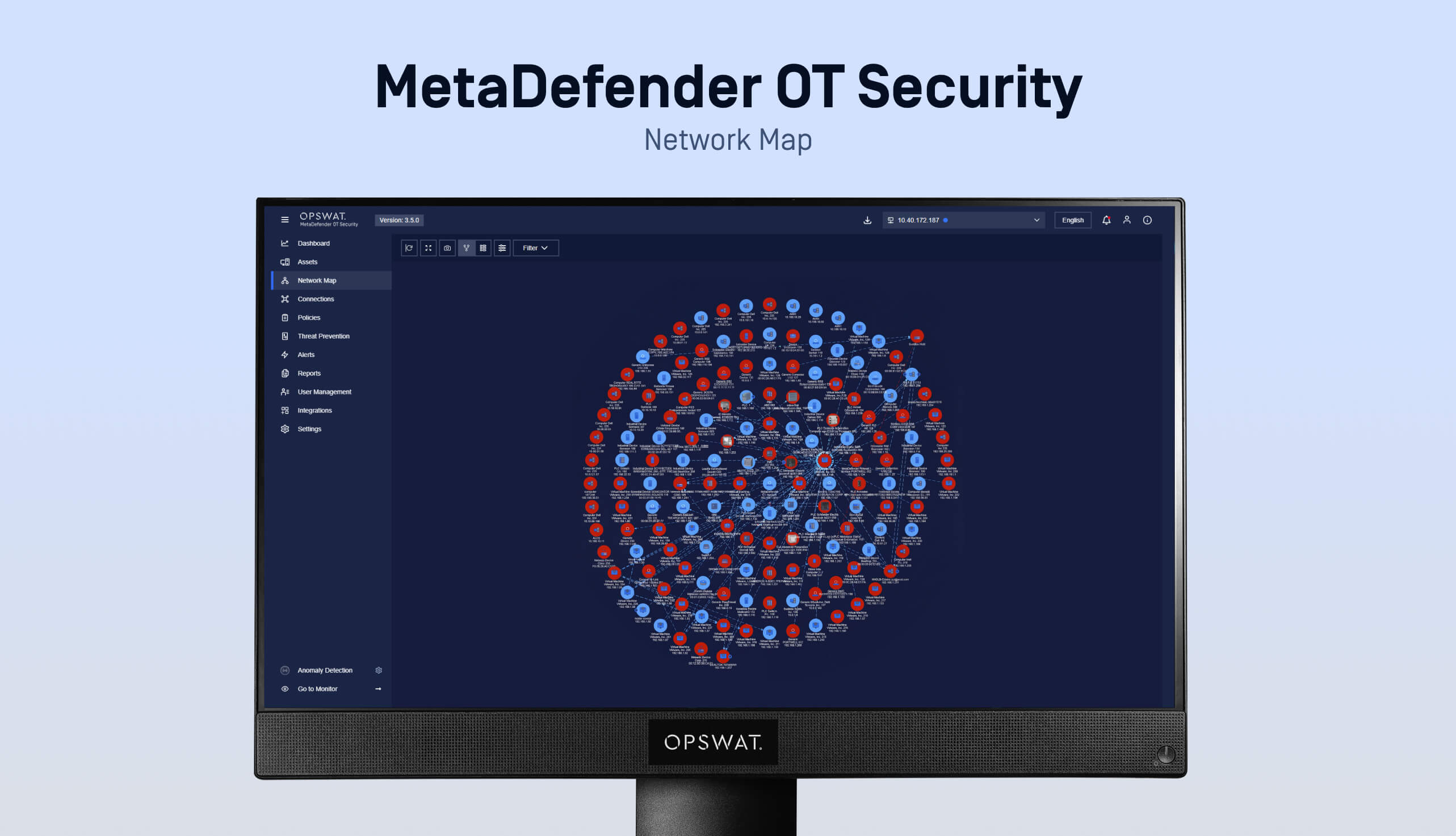
Ügyfelünk, egy vezető pénzügyi szolgáltató cég, éppen ezzel a dilemmával szembesült. Egyrészt a BYOD által biztosított rugalmasságra vágytak, másrészt viszont szükségük volt a szigorú biztonsági szint fenntartásához elengedhetetlen átláthatóságra és ellenőrzésre is. A megoldásOT Security OPSWAT MetaDefender OT Security bevezetése volt, amelyet teljes mértékben integráltak az IT-szolgáltatójuk eszközbevezetési munkafolyamataiba. Ez lehetővé tette az eszközállomány leltározását, a sebezhetőségek kezelését és a fenyegetések felismerését, valamint a központosított jelentéskészítést.
OPSWAT így OPSWAT biztosítani, hogy minden BYOD-eszköz biztonságos legyen, még mielőtt csatlakozna a belső hálózathoz.
A láthatóság, a biztonság és a BYOD-irányelveknek való megfelelés közötti egyensúly megteremtése
Iparáguk jellegéből adódóan ügyfelünk rendkívül érzékeny személyes adatokat, tranzakciós és piaci adatokat kezelt.
Mivel a BYOD-irányelvek elmosják a határt a magáncélú és a munkahelyi eszközök között, nehéznek találták az adatok védelmét anélkül, hogy kinyitották volna a fent említett biztonsági kihívások Pandora szelencéjét.
Konkrétabban az ügyfél a következő területeken szembesült kihívásokkal:
1. Láthatóság
Mivel a munkavállalók saját eszközeiket használták, az ügyfél nem tudta pontosan, milyen szoftverek vagy fájlok találhatók az eszközökön, és ki használja azokat. Mivel nem volt központi rálátása az összes BYOD-végpontra, a szervezetnek szembe kellett néznie a végpontok „vakfoltjaiból” fakadó biztonsági kockázatokkal.
2. Biztonsági intézkedések
A személyes eszközök operációs rendszerének verziói, frissítései és a telepített szoftverek tekintetében eltérőek, ezért nehéz egységes biztonsági szabványokat alkalmazni. Az ügyfél nem tudta egységesen érvényesíteni a vizsgálati és biztonsági irányelveket, ami ismét az eszközök közötti eltérésekből fakadó sebezhetőségeknek tette ki őket.
3. A harmadik felek kockázatkezelésével kapcsolatos nyomás
A személyes eszközök operációs rendszerének verziói, frissítései és a telepített szoftverek tekintetében eltérőek, ezért nehéz egységes biztonsági szabványokat alkalmazni. Az ügyfél nem tudta egységesen érvényesíteni a vizsgálati és biztonsági irányelveket, ami ismét az eszközök közötti eltérésekből fakadó sebezhetőségeknek tette ki őket.
Az ügyfél BYOD-irányelvei felelősségre vonhatósági problémákat okoztak: az eszközök feletti ellenőrzés hiánya megnehezíti a szabályok betartásának garantálását.
Folyamatos eszközleltár és fenyegetésfelismerés a BYOD-hez OPSWAT MetaDefender OT Security segítségével
A szervezet beépítette OPSWAT MetaDefender OT Security az informatikai szolgáltatója eszközbevezetésiOT Security , hogy a következőket tegye lehetővé:
- BYOD-eszközök felderítése és leltározása
- Eszközprofilok létrehozása és osztályozás (típus, operációs rendszer, protokollok)
- Fenyegetés-felismerés
- Központi jelentéskészítés az összes telephelyről
Mind a négy folyamat lezajlik, mielőtt az eszközök hozzáférést kapnának a szervezet belső hálózataihoz.
A megoldás biztosította, hogy az összes alkalmazott és alvállalkozó tulajdonában lévő eszközt a biztonsági irányelveknek megfelelően ellenőrizzék, miközben megőrizték a működési hatékonyságot és a jogszabályi előírásoknak való megfelelést.
MetaDefender OT Security
OT Security MetaDefender OT Security mind a hagyományos informatikai, mind az ipari vezérlőrendszerekre (ICS) jellemző fenyegetésekből fakadó, az operatív technológiai rendszereket érintő kockázatokatOT Security . Az operatív technológiai környezetekben végzi az eszközök felderítését, leltározását és a javítások kezelését. A technológia Enterprise Manager platformja figyelemmel kíséri az informatikai és operatív technológiai hálózatok közötti kapcsolatokat az eszközök azonosítása és a fenyegetések felismerése érdekében.
A BYOD-kockázatok kezelése passzív szkenneléssel és központosított fenyegetés-áttekintéssel
Az ügyfelünkhöz hasonló pénzügyi szervezetek rendkívül érzékeny adatokkal és rendszerekkel dolgoznak. Mivel tisztában voltak a BYOD-irányelvből fakadó kockázatokkal, proaktív módon gondoskodtak arról, hogy a hálózathoz csatlakozó bármely személyes eszköz biztonságos legyen, így védve mind a szervezetet, mind pedig ügyfeleiket.
A MetaDefender OT Security bevezetésével az ügyfél több szinten is javulást tapasztalt:
- BYOD-eszközök vizsgálata és ellenőrzése: Minden személyes eszközt és cserélhető adathordozót automatikusan átvizsgáltak rosszindulatú programok, biztonsági rések és tiltott tartalmak szempontjából, mielőtt hozzáférést engedélyeztek volna.
- Zökkenőmentes IT-integráció: MetaDefender OT Security közvetlenülOT Security az IT-szolgáltató felhasználói regisztrációs és hozzáférési munkafolyamataiba, így biztosítva a biztonsági előírások következetes betartását a működés megzavarása nélkül.
- Központosított áttekinthetőség és jelentéskészítés: A biztonsági csapatok egységes irányítópultokat és részletes vizsgálati jelentéseket kaptak, amelyek valós idejű áttekintést nyújtanak az eszközök állapotáról, az észlelt fenyegetésekről és a javító intézkedésekről.
- Teljes körű riasztási munkafolyamat-kezelés: MetaDefender OT Security egy olyan strukturált munkafolyamatotOT Security , amely a riasztástól a triázson át az incidensig és a reagálásig terjed, lehetővé téve az elemzők számára, hogy szisztematikusan kivizsgálják az észlelt eseményeket, összefüggésbe hozzák a kapcsolódó eseményeket, és dokumentálják a megoldási lépéseket.
- Auditálásra kész megfelelési dokumentáció: Átfogó naplófájlok és jelentések segítették az adatvédelemmel, a kiberbiztonsággal és a harmadik felek kockázatkezelésével kapcsolatos belső auditok lefolytatását, valamint a szabályozási követelmények teljesítését.
Annak biztosítása, hogy minden tranzakció zökkenőmentesen lezajlódjon, anélkül, hogy a BYOD-kockázatok lassítanák a folyamatot
OPSWAT MetaDefender OT Security segítségével a szervezet a működés lelassítása nélkül kezelheti a BYOD-kockázatokat. Miközben továbbra is támogatja a rugalmas munkavégzési gyakorlatokat és megfelel a szigorú szabályozási elvárásoknak, most már egy olyan skálázható megoldással rendelkezik, amely segít megvédeni az érzékeny pénzügyi rendszereket, miközben biztosítja a zavartalan működést.
Ha szervezetének hasonló kihívásokkal kell szembenéznie a hálózatra csatlakozó személyes eszközökkel kapcsolatban, OPSWAT MetaDefender OT Security átfogó eszközáttekintést, folyamatos felügyeletet és fenyegetésfelismerést, valamint strukturált munkafolyamatokatOT Security a riasztások kivizsgálásához és kezeléséhez.
Vegye fel a kapcsolatot szakértőinkkel, és tudjon meg többet arról, hogyan OPSWAT az érzékeny rendszerek és adatok védelmében.