A pénzügyi intézmények egyre inkább ki vannak téve a saját környezetükön kívülről érkező, nagyszabású kibertámadásoknak, amelyek során egyetlen biztonsági rés is több száz szervezetet érinthet. Egy nemrég történt zsarolóvírus-támadás során a támadók hozzáfértek és elloptak több mint 70 bankhoz és hitelszövetkezethez kapcsolódó érzékeny fájlokat, ami akár 1,3 millió embert is érintett; ez jól rávilágít arra, hogy a késedelmes észlelés és a korlátozott átláthatóság hogyan fokozhatja gyorsan a kockázatot az egész pénzügyi szektorban.
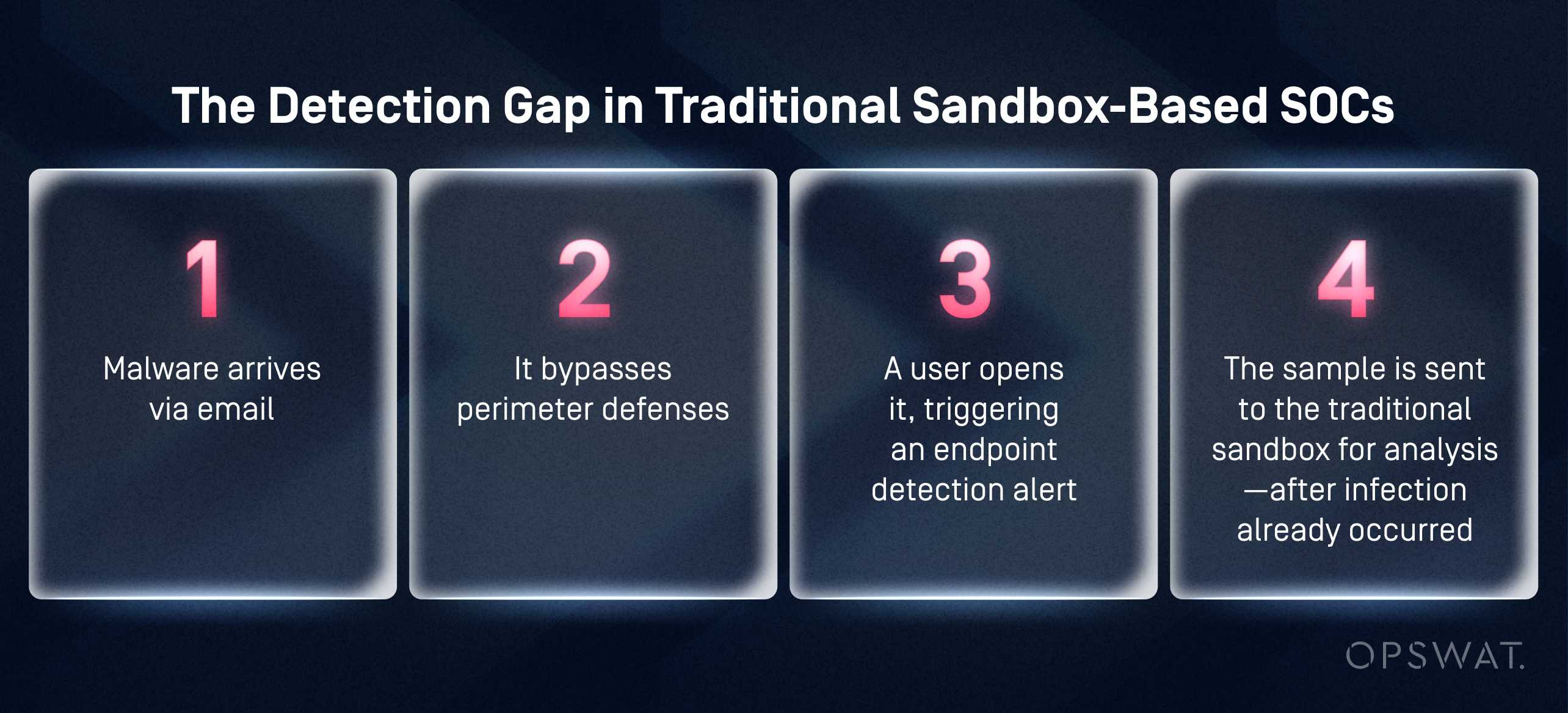
Miért nem tudtak lépést tartani a hagyományos, Sandbox SOC-k?
Ennél a pénzintézetnél a hagyományos SOC-szandboxolás kudarcot vallott, mivel az észlelés túl későn történt. Endpoint csak a kód végrehajtását követően indítottak el elemzést, ami növelte a kockázatot, a reagálási költségeket és a szabályozási kockázatot. A CISO számára ez azt jelentette, hogy az ismeretlen fenyegetések még a megerősítés előtt eljutottak a felhasználókhoz, ami tartós rést eredményezett az észlelés és a megelőzés között.
A SOC számára a méret jelentette a kihívást. Naponta közel 1000 gyanús e-mailt továbbítottak egy virtuális gépen futó sandboxon keresztül a SOAR-automatizálás segítségével. Minden egyes tesztelés jelentős időt és számítási erőforrásokat igényelt, ami állandó várólisták kialakulásához vezetett, ami lassította a vizsgálatokat és meghosszabbította a reagálási időt.
Amikor kiemelt fontosságú incidensek merültek fel, az elemzők kénytelenek voltak felfüggeszteni vagy törölni az automatizált feladatokat, hogy helyet szabadítsanak fel a tesztkörnyezetben. Az automatizálás így nem segítette, hanem gátolta a munkát, ami miatt a biztonsági operációs központ (SOC) kénytelen volt csak reagálni, túlterhelt volt, és képtelen volt megakadályozni a fenyegetéseket, mielőtt azok elérték volna a végpontokat.
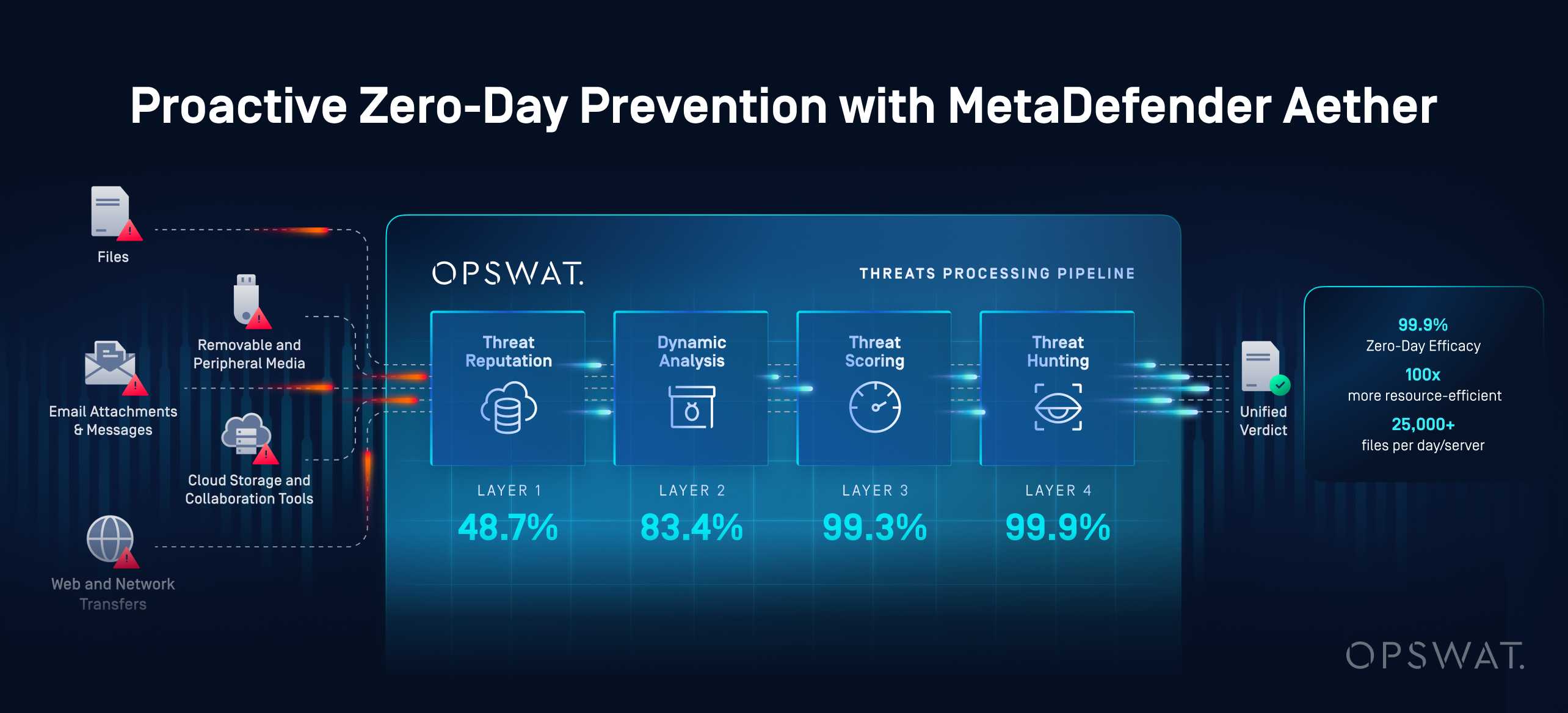
Hogyan tolta balra a zéró napos fenyegetések észlelésétMetaDefender OPSWAT MetaDefender
A szervezet a SOC-kal és a kockázatokkal kapcsolatos kihívásaira úgy reagált, hogy a virtuális gépen alapuló sandbox-rendszerét OPSWAT MetaDefender megoldására cserélte, amely egy utasításszintű emuláción alapuló, egységes zero-day-észlelési rendszer. Ez az architektúraváltás lehetővé tette a biztonsági csapat számára, hogy a dinamikus elemzést a SOC-ból a hálózati peremre helyezze át, ahol a fenyegetéseket még azelőtt meg lehet állítani, hogy azok eljutnának a felhasználókhoz vagy a végpontokhoz.
A hagyományos virtuális gépes futtatással ellentétben MetaDefender a fájlokat utasításszinten futtatja, így kiküszöböli a virtuális gépek indításából adódó késleltetéseket, és csökkenti a virtuális gépek elleni védekezési mechanizmusok általi kijátszás kockázatát. Ez lehetővé tette az intézmény számára, hogy a gyanús fájlokat percek helyett másodpercek alatt elemezze, még nagy e-mail-forgalom mellett is.
A végrehajtás három fő célra összpontosított:
1. Perimeter-first szandboxolás
MetaDefender az e-mail biztonsági átjárókra és a fájlbeolvasási pontokra telepítették, így biztosítva, hogy a gyanús fájlokat a kézbesítés előtt, és nem a végponton történő futtatás után elemezzék.
2. A SOC automatizálásának és méretének helyreállítása
A dinamikus elemzésnek a meglévő SOAR-munkafolyamatokba való közvetlen integrálásával megszűntek a sandboxokkal kapcsolatos sorban álló feladatok, így az automatizált folyamatok az elemzők beavatkozása nélkül is folyamatosan futhatnak.
3. Egységesített zero-day hírszerzés
Minden egyes elemzés hozzájárult MetaDefender beépített fenyegetés-információs folyamatához, amely az emulációs eredményeket, a fenyegetések hírnevét, a pontozást és a gépi tanuláson alapuló hasonlósági keresést ötvözte, hogy fájlonként egyetlen, megbízható értékelést adjon.
Ez a megvalósítás a sandboxingot a passzív incidenskezelő eszközből proaktív peremvédelmi megoldássá alakította át, összehangolva az észlelés sebességét, a rendszer méretét és a kockázatcsökkentést a szervezet működési és szabályozási követelményeivel.
A SOC-teljesítményre gyakorolt mérhető hatás és a kockázatcsökkentés
A virtuális gépeken alapuló szandboxolás MetaDefender való átállásával, valamint a zero-day támadások észlelésének a hálózati peremre való áthelyezésével a szervezet azonnali és tartós működési javulást ért el. Az észlelés gyorsabbá vált, az automatizálás stabilizálódott, és a fenyegetéseket a támadási ciklus korábbi szakaszában sikerült megakadályozni.
MetaDefender által elért mérhető eredmények
| Hatáskör | Mérhető eredmény |
|---|---|
| A SOC automatizálásának teljesítménye | Megszüntettük a lassú, virtuális gépen futó sandbox-kiváltás által okozott SOAR-sorban jelentkező szűk keresztmetszeteket, így az automatizált folyamatok nagy léptékben, folyamatosan futhatnak |
| A vizsgálat sebessége | Az emulációalapú dinamikus elemzés segítségével a fájlok elemzési ideje percekről másodpercekre csökkent |
| Endpoint | Megakadályozta a zero-day fenyegetéseket az e-mailek és fájlok beérkezési pontjain, ezzel jelentősen csökkentve a végpontok megfertőződését és a költséges helyreállítási munkálatokat |
| Az incidenskezeléssel járó munkaterhelés | Csökkentettük a javítást igénylő incidensek számát azáltal, hogy a fenyegetéseket még végrehajtásuk előtt megakadályoztuk |
| Az elemzők hatékonysága | Csökken a homokozó kapacitásának kezelésével és az automatizálási korlátokkal töltött idő, így az elemzők a nagyobb hozzáadott értéket képviselő biztonsági elemzésekre és a fenyegetésekre való reagálásra összpontosíthatnak |
| Felkészültség a zero-day sebezhetőségekre és a szabályozási előírások betartása | Az ismeretlen fenyegetésekkel szembeni proaktív ellenőrzés megerősítése, az audit- és szabályozási elvárásoknak való megfelelés érdekében |
Fenntartható zero-day észlelési modell kidolgozása
A fenntartható zero-day-észlelési modell megakadályozza a fenyegetéseket, a fájlmennyiséghez igazodik, és csökkenti a biztonsági operációs központ (SOC) terhelését. OPSWAT MetaDefender hálózati peremre történő telepítésével a szervezet proaktív megelőzést valósított meg, helyreállította az automatizálást, és olyan, auditálásra kész megközelítést alakított ki az ismeretlen fenyegetések kezelésére szabályozott környezetekben.
A pénzügyi intézmények számára ez a megközelítés nem csupán gyorsabb észlelést jelent. Skálázható, auditálásra kész modellt biztosít a zero-day kockázatok kezeléséhez, csökkentve ezzel a biztonsági operációs központok (SOC) csapatainak operatív terhelését, és megerősítve a kritikus fájláramlások biztonsági ellenőrzéseibe vetett bizalmat.MetaDefender bemutatja, hogyan alakíthatja a modern, utasítás-szintű szandboxolás és az egységes fenyegetési hírszerzés a zero-day észlelést mérhető üzleti előnnyé.
Készen áll arra, hogy megvédje kritikus fájlkezelési folyamatait, és még időben megakadályozza a zero-day fenyegetéseket?