Mivel a kiberfenyegetések egyre nagyobb méreteket öltenek és egyre kifinomultabbá válnak, az APRA CPS 234. számú prudenciális szabványa – az információbiztonságról szóló szabvány – továbbra is az ausztrál pénzügyi intézmények információbiztonsági irányításának sarokköve marad. Ez a szabvány kötelező követelményeket fogalmaz meg annak biztosítására, hogy a szabályozott szervezetek erős, arányos és ellenálló információbiztonsági képességeket tartsanak fenn.
A CPS 234-et a Prudential Practice Guide CPG 234 kiegészíti, amely gyakorlati útmutatást, példákat és kockázatkezelési szempontokat tartalmaz , hogy segítse a szervezeteket a CPS 234 hatékony értelmezésében és végrehajtásában. Míg a CPS 234 meghatározza, mit kell tenni, addig a CPG 234 arra összpontosít, hogy mindez a gyakorlatban hogyan valósítható meg.
Mindkét dokumentum kiemeli a többszintű védelmet, a szigorú megelőző ellenőrzéseket, a folyamatos felügyeletet és a bizonyítható biztonságot. Ezek mind olyan területek, ahol OPSWATfenyegetésmegelőző és zero-trust megoldásai kulcsfontosságú szerepet játszhatnak.
CPS 234 és CPG 234: Hogyan működnek együtt?
- A CPS 234 végrehajtható és eredményorientált szabvány, amely előírja a szervezetek számára, hogy olyan információbiztonsági rendszert tartsanak fenn, amely megfelel a környezetüknek, valamint az adataik és eszközeik kritikus fontosságának.
- A CPG 234 egy nem kötelező érvényű iránymutatás, amely kiegészíti a CPS 234-et, és bevált gyakorlatokra vonatkozó példákat tartalmaz az irányítás, az ellenőrzési mechanizmusok bevezetése, a tesztelés és az incidenskezelés terén. Ezenkívül ösztönzi a megelőző, felderítő és korrekciós ellenőrzési mechanizmusok alkalmazását, különös hangsúlyt fektetve a fenyegetések lehető legkorábbi megakadályozására.
A CPG 234 többször is hangsúlyozza:
- többszintű megelőző ellenőrzések,
- a behatolási pontok támadási felületének csökkentése,
- az adatáramlás és a végpontok ellenőrzése,
- folyamatos ellenőrzés, tesztelés és minőségbiztosítás,
- valamint gyakorlati bizonyítékok az igazgatóság és a szabályozó hatóságok felügyeleti tevékenységének alátámasztására.
Ezek a témák szorosan illeszkednek OPSWAT„Ne bízz egyetlen fájlban sem, ne bízz egyetlen eszközben sem” elvéhez.
Hogyan OPSWAT Secure intézmények Secure
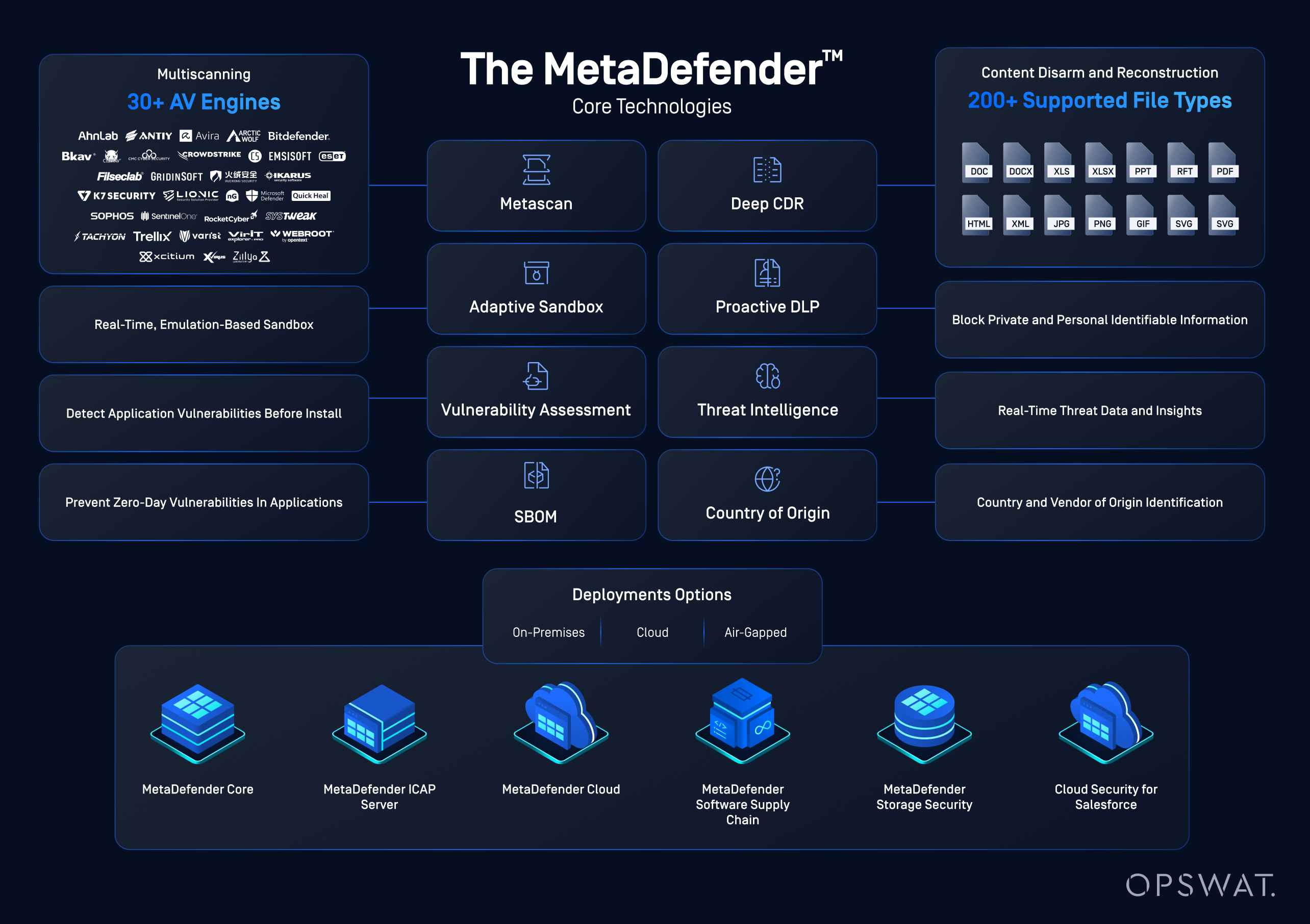
OPSWAT MetaDefender többszintű megelőző védelmet biztosít számos támadási csatorna ellen:
Multiscanning Deep CDR™ technológia
A CPG 234 kiemeli annak fontosságát, hogy többféle szintű és típusú ellenőrző mechanizmust vezessenek be, hogy amennyiben egy ellenőrző mechanizmus meghibásodik, a többi korlátozza az információbiztonsági incidens hatását.
OPSWAT többféle vizsgálati technológiát OPSWAT , hogy átfogó, többszintű fájlellenőrzést biztosítson. Több mint 30 kártevőellenes motort használ, amelyek szignatúrákat, heurisztikát, gépi tanuláson alapuló felismerést és mesterséges intelligenciával működő fenyegetésfelismerő motort alkalmaznak, valamint fájlhírnév- és hash-elemzést is igénybe vesznek az ismert fenyegetések gyors besorolásához.
Az ismeretlen és zero-day támadások esetén a Deep CDR™ technológia eltávolítja az aktív vagy rosszindulatú tartalmakat, majd a fájlokat biztonságos, használható formátumba alakítja át. A „soha ne bízz, mindig azonosíts” elv alapján működik.
Secure és adatátvitel
A CPG 234 szigorú ellenőrzést ír elő a rendszerek, harmadik felek és bizalmi zónák közötti adatmozgás tekintetében. OPSWAT az átjárókban és az átviteli pontokon OPSWAT és megtisztítja a fájlokat, hozzájárulva ezzel az adatok bizalmas jellegének és integritásának védelméhez. MetaDefender ICAP különféle hálózati eszközökön keresztül továbbított adatok vizsgálatát biztosítja.
A pénzügyi szektor különböző intézményei által online módon üzemeltetett termékek és szolgáltatások kihasználhatják API MetaDefenderREST API a MetaDefender Storage Security szolgáltatással kombinálva biztosíthatják a fájlfeltöltések biztonságát.
Sebezhetőségi és Software értékelés
A CPG 234 előírja a gyenge pontok proaktív felismerését. OPSWAT file-based vulnerability assessment segítenek a kockázatos vagy elavult szoftverek azonosításában, még mielőtt az alkalmazásokat a környezetbe telepítenék. Ezen felül OPSWATSBOM-ja (Software of Materials) hozzájárulhat az alkalmazásfejlesztés biztonságosabbá tételéhez a DevOps módszertan alkalmazásával.
Ezek az ellenőrzési intézkedések segítik annak igazolását, hogy az információbiztonsági képességek a CPS 234 előírásainak megfelelően arányban állnak a kockázattal.
Az identitáskezelés és a hozzáférés erősítése
Mind a CPS 234, mind a CPG 234 kiemeli a nem felügyelt eszközök, a távoli hozzáférés és a harmadik felekhez való csatlakozások jelentette kockázatokat. A CPG 234 kifejezetten azt javasolja, hogy a rendszerekhez és adatokhoz való hozzáférés megadása előtt ellenőrizzék a végpontok biztonsági állapotát.
OPSWAT MetaDefender az eszközök állapotának felmérésével eszközalapú, zéró bizalmi hozzáférés-vezérlést tesz lehetővé. A hozzáférés engedélyezése előtt ellenőrzi az operációs rendszer állapotát, a biztonsági szoftvereket, a titkosítást, a földrajzi helymeghatározást, a sebezhetőségeket és a frissítések kezelését.
A következőket támogatja:
- a hozzáférés-ellenőrzés szigorúbb érvényesítése
- a nem biztonságos vagy nem felügyelt végpontokból származó kockázat csökkentése
- valamint a CPG 234 távoli hozzáférésre és harmadik felekkel való kapcsolódásra vonatkozó ajánlásainak jobb figyelembevétele.
Supply Chain átláthatósága
A CPS 234 előírja, hogy a saját fejlesztésű szoftvereket készítő szervezeteknek a szoftverfejlesztési életciklus (SDLC) részeként figyelembe kell venniük a biztonsági ellenőrző intézkedéseket. A CPG 234 ezt megerősíti azzal, hogy hangsúlyozza a szoftverbiztonságra vonatkozó folyamatos megközelítés szükségességét . Ez magában foglalja a követelmények meghatározását, a tervezést, a kiválasztást és a konfigurálást, valamint azt, hogy mely szabványokat és irányelveket kell betartani.
Az OPSWATMetaDefender Software Supply Chain segít az alkalmazásfejlesztőknek ellenőrizni, hogy a forráskód, a könyvtárak és a harmadik féltől származó függőségek átvizsgálásra kerültek-e, és mentesek-e minden rosszindulatú komponenstől, sebezhetőségtől vagy beágyazott titkos adattól, amelyek véletlenül a forráskódban maradhatnak.
Ez közvetlenül megfelel az APRA szoftverbiztonsággal és az ellátási lánc kockázatkezelésével kapcsolatos elvárásainak.
- A szoftverbiztonsági intézkedések erősítése a szoftverfejlesztési életciklus (SDLC) egészében.
- Az SBOM használata az ellátási lánc átláthatóságának javítása érdekében.
- Beépítés a DevOps munkafolyamatba.
- A jelentéstétel és az irányítás kockázatalapú értékelésének támogatása.
Az incidensek felismerésének, kezelésének és jelentésének gyorsítása
A CPS 234 előírja az információbiztonsági események időben történő felismerését és bejelentését. A CPG 234 ezt továbbfejleszti azzal, hogy ösztönzi a megelőző ellenőrzések, a felügyeleti platformok és a reagálási folyamatok szoros integrációját.
Bár OPSWAT nem SIEM- vagy SOC-platform, a következőképpen integrálódik a tágabb értelemben vett biztonsági ökoszisztémákba:
- a fenyegetési információk és az észlelési eredmények továbbítása a SIEM- és SOAR-eszközökbe,
- a biztonsági események kontextusának kiegészítése fájl-, eszköz- és sebezhetőségi információkkal, valamint
- ezáltal gyorsabb kivizsgálást és reagálást tesz lehetővé.
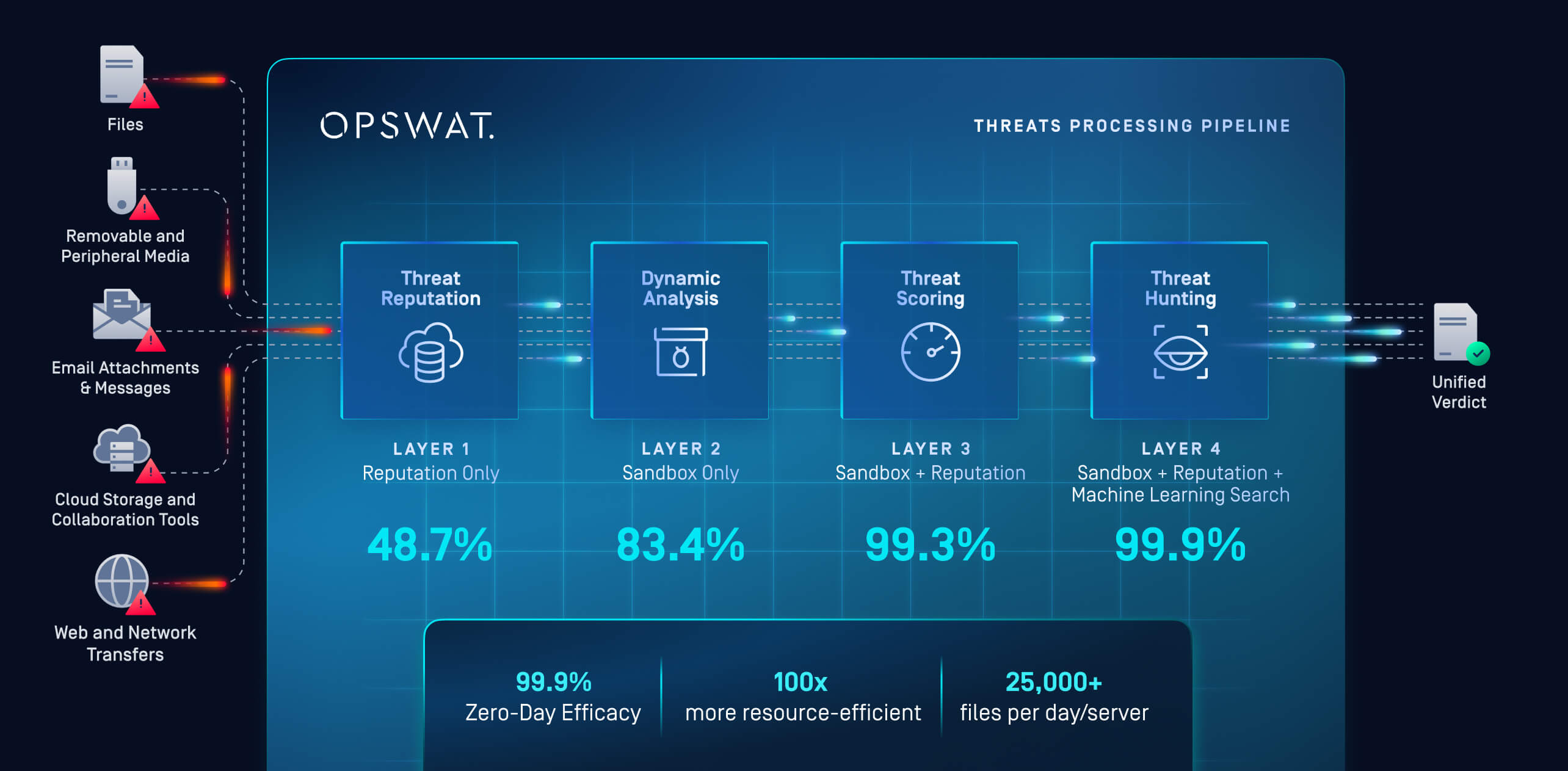
OPSWAT MetaDefender a rosszindulatú programok elemzése során 20-szor gyorsabb, mint a hagyományos sandbox-technológiák. Ez segíthet a biztonsági operációs központok (SOC) csapatainak abban, hogy javítsák a reagálási idejüket a biztonsági incidensek felismerése és kezelése során.
A következő elemek kombinációját használja:
- Fenyegetés-hírnév – Valós időben vagy offline módban ellenőrzi az URL-eket, IP-címeket és domainneveket a rosszindulatú szoftverek, az adathalászat és a botnetek felderítése érdekében. Megakadályozza az újrahasznosított infrastruktúrák és a széles körben elterjedt rosszindulatú szoftverek használatát, és arra kényszeríti a támadókat, hogy változtassák meg az alapvető azonosítókat.
- Dinamikus elemzés – Egy emulációalapú sandbox (amely a rosszindulatú programokat az utasítások szintjén történő értelmezéssel elemzi, anélkül, hogy teljes virtuális gépet futtatna) elemzi a fájlokat a rejtett fenyegetések, például a zsarolóvírusok felderítése érdekében. Felfedi a programelemeket, a betöltő láncokat, a szkript logikáját és a felderítés elkerülésére szolgáló taktikákat.
- Fenyegetésértékelés – A viselkedési mutatók, a hírnévvel kapcsolatos kontextus és az észlelési logika összefüggéseinek figyelembevételével bizalmi szintű kockázati pontszámot rendelünk a fenyegetésekhez, ami segít a biztonsági operációs központok (SOC) csapatainak a valóban fontos események prioritásba sorolásában. A rendszer célja a rosszindulatú viselkedésmódok felismerése és elemzése, különös tekintettel a MITRE ATT&CK keretrendszerben szereplő legfontosabb taktikákra.
- Fenyegetésfelkutatás – A „Threat Pattern Correlator” kereső funkció az ismeretlen mintákat összekapcsolja az ismert kártevőcsaládokkal, infrastruktúrákkal és kampányokkal, lehetővé téve ezzel a proaktív felkutatást és a visszamenőleges elemzést.
OPSWAT MetaDefender Detection & Response (NDR) platformja nagy áteresztőképességű DFI (Deep File Inspection) funkciót biztosít a fenyegetések és az adat szivárgás megelőzéséhez, felderítéséhez és felkutatásához.NDR MetaDefender NDR a hagyományos SOC-elemző szakértői tudásának automatizálása és kiterjesztése. MetaDefender NDR a Deep File Inspection technológiát egyedülálló fenyegetés-információs forrásokkal, valamint egy tapasztalt, gépi tanulással támogatott szignatúra-fejlesztő csapattalNDR .
A megoldás elsősorban az internetről letöltött vagy e-mailben kapott fájlok azonosítására és elemzésére összpontosít a rosszindulatú kódok felderítése érdekében. MetaDefender NDR az összes HTTP- és SMTP-hálózati forgalmi munkamenetet a hálózati csapokról, átirányításokról vagy csomagfogási fájlokból, majd mélyreható fájlvizsgálatot hajt végre a rögzített adatokon.
A DFI segítségével az elemzők gyorsan kiszűrhetik a rosszindulatú tartalmakat, riasztásokat generálhatnak azokról, illetve fenyegetéskeresést végezhetnek a gyanús tartalmak kiválasztása érdekében, hogy azokat részletesebb elemzésnek vessék alá.
A legtöbb hálózati behatolás-érzékelő rendszerrel (NIDS) ellentétben MetaDefender NDR arraNDR , hogy a fájlattribútumok, a fájltartalom és a hálózati jellemzők kombinációját natív formátumukban elemezze. A rejtett adatokat – például a fájlformátumokba ágyazott és/vagy tömörített adatfolyamokat, amelyeket gyakran használnak az NIDS-ek által végzett észlelés kijátszására – a rendszer kibontja és normalizálja, hogy ezzel maximalizálja a végrehajtott, szignatúra-alapú vizsgálati módszerek hatékonyságát.
Ezen felül, MetaDefender NDRnem egyetlen funkcióval javítja a sebességet, hanem a SOC munkafolyamatának akadályait szünteti meg:
- Korábbi felismerés (mélyreható vizsgálat + fenyegetési információk)
- Gyorsabb elemzés (kontextusban gazdag, összefüggő adatok)
- Gyorsabb reagálás (automatizálás + integrált műveletek)
- Hatékony jelentéskészítés (SIEM-kompatibilis kimenetek)
Lényegében MetaDefender NDR egyszerreNDR a támadók rendszerben való tartózkodási idejét és az elemzők munkaterhelését, így az észlelés nem késleltetett vizsgálatot, hanem azonnali, cselekvésre késztető reagálást eredményez.
Az APRA információbiztonsági szabványainak gyakorlati biztonsági eredményekké alakítása
A CPS 234 meghatározza az APRA által elvárt szabályozási eredményeket, míg a CPG 234 a gyakorlatban történő megvalósításukhoz szükséges útmutatást tartalmazza. Együttesen kiemelik a proaktív kockázatcsökkentés, a többszintű ellenőrzés, a folyamatos tesztelés és a bizonyítható biztosíték fontosságát.
OPSWATfenyegetésmegelőzési, zéró bizalmi hozzáférési és ellátási lánc-értékelési megoldásai az alábbiak révén segítik a szervezeteket e követelmények gyakorlati megvalósításában:
- a támadási felület csökkentése a legfontosabb behatolási pontokon,
- a bevált gyakorlatokhoz igazodó megelőző ellenőrzések megerősítése,
- az ellenőrzésekre alkalmas bizonyítékok előállítása az ellenőrzések hatékonyságáról, valamint
- valamint az incidensek hatékony felismerését és kezelését szolgáló folyamatok támogatása.
Az APRA által szabályozott szervezetek esetében OPSWAT bevezetése OPSWAT az információbiztonsági szabványok végrehajtását, és hozzájárul a jogszabályi követelmények és a gyakorlati kiberbiztonság közötti szakadék áthidalásához.
Ha szervezete az APRA szabályozása alá tartozik, vegye fel velünk a kapcsolatot, és tudjon meg többet arról, hogyan OPSWAT a szabályoknak való megfelelést.

